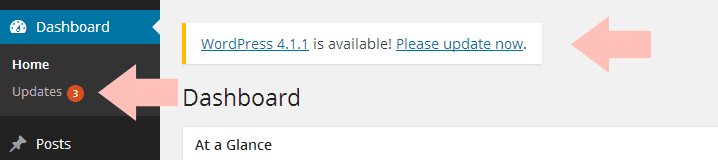
Have you ever seen this before?
If you use self-hosted WordPress, you have. You know what baffles me? People who ignore this message. Sometimes for years.
Yes, I’ve seen some people using WP versions that are YEARS out of date.
Isn’t that just completely baffling? Let’s put aside all the “big” reasons to update WordPress (like security). There’s one thing that I just don’t get… That little, red-ish orange-ish updates bubble on the left bugs the shit out of me. I can’t stand to be inside a WordPress installation that has that little bubble. It just irks me.
Same goes for the “WordPress x is available! Please update now.” message. If it were me, I would be annoyed if I saw that every single time I logged in. So what would I do? Click the button and perform the update.
I just don’t understand how some people can ignore that message! For years!
I recently (after WP version 4.x) came across a person who was still using the old WordPress interface. You know, the one that looked like this:
That means they looked at that annoying little bubble for about 2.5 years. TWO AND A HALF YEARS.
But it’s not just an annoying bubble—outdated WordPress is insecure.
There are two reasons why WordPress gets updated:
- To introduce new features.
- To fix things.
#1 isn’t necessary. It’s nice, and it’s what helps WordPress compete with other platforms, but ultimately it’s not required. You can live without extra features.
But #2 is super important. Some things that get fixed are things you may never notice, like little glitches that only happen under certain circumstances. But other things are huge security vulnerabilities. Just look at this big list of WordPress security vulnerabilities. That’s a list of all the things that have been wrong with WordPress. Here are just a few:
wp-includes/class-wp-customize-widgets.php in the widget implementation in WordPress 3.9.x before 3.9.2 might allow remote attackers to execute arbitrary code via crafted serialized data.
WordPress before 3.6.1 does not properly validate URLs before use in an HTTP redirect, which allows remote attackers to bypass intended redirection restrictions via a crafted string.
wp-includes/functions.php in WordPress before 3.6.1 does not properly determine whether data has been serialized, which allows remote attackers to execute arbitrary code by triggering erroneous PHP unserialize operations.
Cross-site scripting (XSS) vulnerability in swfupload.swf in SWFupload 2.2.0.1 and earlier, as used in WordPress before 3.5.2, TinyMCE Image Manager 1.1 and earlier, and other products allows remote attackers to inject arbitrary web script or HTML via the buttonText parameter, a different vulnerability than CVE-2012-3414.
Those are all ways that hackers can get into your site, destroy your site, change your site, or take down your site. By not updating WordPress, you’re leaving yourself vulnerable to those attacks.


I have a recurring task in my task manager app to install any updates anywhere every Sunday. Between reading about WordPress vulnerabilities and working for a company that discovers advertising fraud (frequently because of outdated apps, browser plugins, and poorly maintained servers), I would get itchy going any longer than that. I’ll install an update as soon as I notice it, but this reminds me to check.
That’s wonderful Brittany. It’s always good to remember your updates!
I always do. The notification taunts me until I do. Lol!
Same here! I mean, I’d update anyway, but the notification REALLY bugs me so that alone would encourage me to do it, haha.
Wow. That’s crazy! How can people stand to look at the notifications for so long. They annoy me. I always update anytime those boxes show up because I get all OCD.
I KNOW!! I totally get OCD too. I can’t stand to look at them. I cringe whenever I login to a client’s site and see like 203572309523 update notifications.
Ha! That’s going to happen to you this weekend. I updated my wordpress and my theme a couple of months ago, and it broke my WHOLE WEBSITE because the designer had all of these features turned off, and then she was the slowest person ever getting back to fix it. So not until I know what’s going to happen and can fix it myself will I do the latest update!
Oh no!! 😛 Haha.
I’m so sorry about what happened with your website. That’s horrible!!
Hey, not your fault at all! But just another one of the reasons why I sought you out! 🙂 So excited for the switch!
I’m the same when it comes to updates – not just site ones but others as well… I’m glad I’m not the only one!
Does Book Host automatically update the WordPress versions or would we have to do that manually? Just wondering.
Yep, on Book Host I handle all updates for you. 🙂 That includes WordPress itself, plugins, and themes.
I admit it, sometimes I am terrible about this. But only like 2 weeks terrible, not years. I’m lazy.
I’m also that person whose email app on her phone has the unread messages badge. It currently says 118 LOL.
As long as it’s not a big security update, two weeks isn’t too bad. 😛
Hahaha I love that you’re so upset about the little red bubble because I COMPLETELY UNDERSTAND. I can’t with those things, I just can’t. I have to update everything right away because the warnings really bother me in an OCD way. Plus, security. But mostly it just bothers me.
THE RED BUBBLE IS HORRIBLE!!! Hahaha.
It’s all about that notification bubble! That is the reason why I am so good at updating all the things. Those little bubbles drive me bonkers and I have to take care of them.
I totally agree! I can’t stand that horrible little bubble. They must do that on purpose, don’t you think?
I admit I ignore plugin updates, or WordPress updates. But I don’t ignore them for YEARS! Maybe a couple of days, a week at the most. The only “updates” still hanging out there are those themes we talked about a while ago LOL. And yes, the reddish-orange circle is starting to really bug me. I’ll have to do something about that 😉
Tsk, tsk! You should at least check to see if it’s an important security update before you let them sit for too long. Usually, security holes look like this:
1. Someone discovers the hole.
2. Someone starts EXPLOITING the hole (hacking sites, etc.).
3. The plugin creator becomes aware of it and fixes it (thus issues an update).
4. But once that happens, MORE people know about the flaw.
5. Other hackers join in and start finding sites they can exploit.
So #4 and #5 happen in the few days/weeks after the plugin is updated (usually). It helps to at least look at the changelog for anything that says like “Security fix” or “Fixed exploit” or things like that.
I would basically update them whenever they appear on the dashboard. But if it is a major update of WordPress, I would make sure my plugins are compatible with the latest version before I upgrade it.
I guess for those who didn’t upgrade their WordPress installation and update the plugins just don’t know the importance and significance of it.
That’s awesome, Regina! And if there’s a security update for WordPress and one of your plugins isn’t compatible, it’s much better to just deactivate that plugin until it’s updated and upgrade WordPress. It’s better to lose a plugin than be vulnerable!
Thanks for highlighting it!
I do. And I cross my fingers every time. Which plugin won’t work this time?
To be honest, if a plugin breaks with a WordPress update, that means the developer isn’t on top of the plugin or regularly maintaining it, and thus you may not want to use it anyway. 😉
Once I figured out how to back up my blog first, I updated WordPress when the last update went through. And I’ll update plugins when I’m notified about those. But what bugs me is that they also give me the little red bubble for updates to themes I don’t have and I’m not using. Is there some reason I need to update those?
Well if you’re not using those themes, you can just delete them. 🙂
I always do. Sometimes WP automatically updates, so that’s cool. 😀
Yeah it’s great that they’ve started doing that for security updates!
Yeah, I always, always update WordPress. I feel like something bad will happen if I don’t (something will stop working, I’ll get hacked again) so I make sure to do it right away. And yes, I hate seeing the numbers and messages at the top of the screen saying I have updates! Super annoying but I guess effective 🙂
That’s great Zareena. If WordPress issues a security update/patch, then something bad could indeed happen if you don’t upgrade!
I think mine updates automatically. If it doesn’t, I always do it myself immediately. 🙂
Yeah WordPress has started issuing smaller patches automatically, which is fantastic. I think you still have to do big upgrades on your own (like from 3.9 to 4.0, for example).
It baffles me that people don’t update. I always allow all the updates immediately – from the moment that orange bubble appears. One, because it’s annoying. And two, because they introduce updates for a reason. I’ve never even noticed anything changing after an update, so that can’t be a reason why you wouldn’t want to update. It’s easy, it’s fast. It’s safe. Why not?
It baffles me too, Inge! I just can’t comprehend it. It’s so easy to do, too.
A lot of people don’t like to do it because their plugins may break. But if that happens, it’s a sign that you shouldn’t be using those plugins in the first place because the developers aren’t updating or maintaining them for new releases.
I always update WordPress as soon as I spot an update. As you said it, they always fix bugs & security leaks… ut I noticed that a lot of people do not update their software. I don’t know why… I think they have some irrational fear that it will not work after an update.
Sometimes things don’t work (plugins, etc.) but if that’s the case, they should stop using those plugins anyway. It means the developer isn’t actively maintaining them, which is never a good sign. That means it’s time to move on and find an alternative that’s being maintained and updated regularly.
It never happened to me. I guess I use popular plugins that are regularly maintained. Or those which are written properly so they do not create problems.
Yep that’s very possible. I find that most of the super popular plugins with thousands (or hundreds of thousands) of downloads are usually maintained very well, and often by a whole community of people rather than just one person.
I always update mine as soon as I see it. I don’t come to my blog daily, but always at least every 3 days. I can’t stand the bubble, so I update them right away. I know it’s important, but it’s honestly mostly to ditch the damn bubble. It’s like my alarm clock. I wake up because snoozing means I have to hear it yelling at me again.
Hi, I work for my university newspaper and they haven’t updated their wordpress yet because it says that it will affect all files and folders included in the main WordPress installation. This includes all the core files used to run WordPress. If you have made any modifications to those files, your changes will be lost. – What exactly does this mean? Will we have to change everything to get it back to how it used to look? The website is pluto-online.com I have been put in charge with getting a new theme and updating everything but I don’t want it to go wrong
Hi Emmi,
Only the main WordPress installation files are affected by an upgrade. If you haven’t edited these .php files (which you should NEVER do anyway) then you don’t have to worry about anything.
For example, plugins and themes are not changed, edited, or affected by a WordPress upgrade.
I always update wordpress and any plugins as soon as I see the update, I think wordpress even updates automatically nowadays. Once I started self hosted wordpress I heard a few times that not updating is a security risk and since then I always update as soon as possible and indeed I can’t stand that buble telling me I have to update.
I’m with you, that little update icon bothers me too. But really, I wonder if people are doing it on purpose or if they just don’t know what to do so they don’t bother?
My webhost automatically updates WordPress for me, so I never see the orange bubble for that update. I install the updates for my plugins when the bubble appears and tells me they’ve updated though. Longest I usually go before I update those is a day or so, depending on how busy I was when I saw the alert. But usually it’s right away.
I don’t understand why you -wouldn’t- want to update when it tells you there’s one available. If for no other reason, I wouldn’t want to see the orange bubble every day. It would annoy and distract me too much!
Um…let me give you another perspective of why some of us don’t want to upgrade “NOW”.
Because WordPress.org is known to bring sometimes features that limit the capabilities of our editing. How about the latest one – I was very happy with version 3.8 and when I finally upgraded, boy I’m so sorry I did it.
WordPress removed the capabilities of advanced photo editing (e.g. setting margins, paddings, etc), so unless you’re html savy (which not everyone is), to add CSS styles and whatnot to your blog, you need to use a plugin for something that was there in WordPress by default for over 4 years. I mean really???
There are tons of pissed off users who wish they hadn’t upgraded now (and consider me one among them).
Would you rather:
1. Update and be safe.
2. Not update and get hacked.
You can read an article about some of the logic behind why it was removed here: http://wptavern.com/how-the-advanced-image-editing-properties-contributed-to-wordpress-theme-lock-in
But as you said, there is now a plugin available, so upgrading didn’t end up being a problem. 😉
Yep, that’s what I ended up doing, but needless to say, I’m angry – along with lots of other people – at the folks behind WP with their dumb logic. And I know still a lot of them haven’t upgraded their WP – just check the WordPress.org forums. Personally I’ve never been hacked since working on WP (from the very early day – yeah many years ago), so I guess I don’t feel the ‘urgency’ – although I understand why it’s a good thing. But I digress 🙂
If you use outdated WordPress and they issued a security patch, it only takes one nasty guy to realize this and exploit it. 😉
I always update right away. I don’t have it set to automatically update because I like being sure my backups are current, but like you said, I don’t want a security risk. Thanks, Ashley!
My host automatically updates WordPress for me within 24 hours of an update. I still have to update plugins myself. I do it as soon as I see that bubble because it drives me crazy. It’s like the bubbles on my iphone, they must be taken care of immediately.
I have a hunch that people don’t update in part because they don’t think that their lil ole site is worth a hacker’s interest. My husband’s personal training site – a site that got no traffic because he wasn’t active and wasn’t selling anything – got hacked by a “Free X” group of some sort (the X isn’t important here). His site was gone, and was replaced by a “You’ve been hacked” statement splashed across an eerie image. Ugh.
Every site is worth a hacker’s interest. 😉 There are so many different motives behind hacking and most of them aren’t “just for fun”. There’s real motive there. It usually involves some kind of money/profit. Your site doesn’t have to be huge or popular in order for them to profit off hacking you.
– They’ll redirect your site traffic to their site where they sell viagra or whatever (stealing your visitors).
– They’ll use your server to aid in a DDoS attack somewhere else (stealing your resources). Or they’ll use your server to help hide their identity while they do something sketchy/illegal.
– They’ll use your server to send out tons of spam emails. This is related to the previous point. By using YOUR server and not their own, it’s harder to trace the spam back to this person since the server isn’t under their name.
– To distribute viruses to your visitors.
– Then there’s vandalism or “just for fun” or “just to prove a point” hacking.